FireEye released the Mandiant® Security Effectiveness Report 2020 which reveals data about how well organizations are protecting themselves against cyber threats and the overall effectiveness of their security infrastructure. The report summarizes the results of thousands of tests performed by experts from the Mandiant Security[…]
Category: Blog
The curious case of the Raspberry Pi in the network closet, how we found, analyzed (with the help of Reddit) and in the end caught the culprit of a malicious device in our network
NOTE: This document incomplete, still DRAFT Mode… The intelligence, in terms of security, is a collection of security-related information which when analysed provides meaningful foresight. The threat intelligence likewise is an analysis of information collected about the cyber threat so[…]
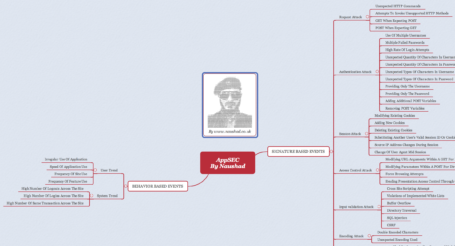
Application security encompasses measures taken to improve the security of an application often by finding, fixing and preventing security vulnerabilities. From the risk management strategic point of view, the mitigation of application security risks is not a one time exercise;[…]
Many of your company’s most valuable assets are at risk to criminal activities carried out on the Dark Web – and you don’t even know it. Turning a blind eye to this will impact your: Brand and reputation Customer loyalty[…]
Canada’s First Cybersecurity Law | BILL C-59 – Secure Knowledge Management SUMMARY Part 1 enacts the National Security and Intelligence Review Agency Act, which establishes the National Security and Intelligence Review Agency and sets out its composition, mandate and powers. It repeals the[…]
List of Free Hacking books PDF. Ethical Hacking, Hacking books pdf, Hacking ebooks free download, hacking ebooks collection, Best Hacking eBooks. This list for everyone who is interested in ethical hacking, beginners or professionals both. These top 100 hacking books[…]
Here is my personal collection of IP addresses engaging in abusive behavior on the networks, for webmasters and sysadmins to block IP addresses engaging in abusive behavior on their networks.
Live webinar: http://goo.gl/VVKxS3 Way back in 2000 it was common practice to spend considerable time configuring and tinkering the plumbing of what we today call cyberspace. The technology was embryonic, immature and often hours were spent ensuring nothing broke and[…]
Basic rate-limiting middleware for Express. Use to limit repeated requests to public APIs and/or endpoints such as password reset. A brute-force protection middleware for express routes that rate-limits incoming requests, increasing the delay with each request in a fibonacci-like sequence[…]
|--Although you should be able to work out who I am, I don't really care, as I can work out who you are. So beware of leaving footprints.--|