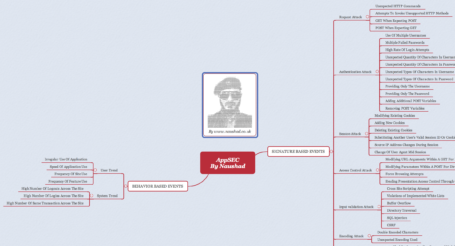
The challenges security managers face never stand still. Threats change, new technologies appear, global conflicts arise, economic cycles drive business change – the trends in each of these areas have a profound and complex impact on successful security strategies. Here is my personal blog will highlight and analyse emerging security trends and discuss new data from worldwide-and-deepweb, government sources, the security community and security events. Find the meaningful events and predictions amidst all the hype and noise.
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
What are cookies?
Cookies are small pieces of text stored on your computer when you visit almost any website. Companies use them to:
- Verify your identity, to ensure your security and privacy
- Determine the browser and settings you are using to provide optimised content
- Understand the way you navigate through websites, so firms can make improvements
- Help site owners and third-party advertisers tailor content to your preferences
We also use social media buttons and/or plugins on this site that allow you to connect with your social network in various ways. For these to work the following social media sites including;
-
- Linked In
-
- YouTube
will set cookies through our site, which may be used to enhance your profile on their site or contribute to the data they hold for various purposes outlined in their respective privacy policies.
GOOGLE CHROME
There are multiple levels of cookie enablement in Chrome. For more information, click here.
INTERNETEXPLORE
There are multiple levels of cookie enablement in Internet Explorer. For more information, click here.
MICROSOFT EDGE
There are multiple levels of cookie enablement in Edge. For more information, click here.
MOZILLA FIREFOX
There are multiple levels of cookie enablement in Firefox. For more informaiton, click here.
OPERA
There are multiple levels of cookie enablement in Opera. For more information, click here
SAFARI
For more information, see the Safari user guide.