InfoSec talks: 2008 Computer science, Cyber Security and Management (CSM) – The MSc in Cyber Security and Management is designed for those wishing to develop a career as cyber security professionals, or to take a leading technical or managerial role in[…]
Hackers are hijacking internet routers used in small to large businesses and homes to become a huge Botnet that they can use to launch Distributed Denial of Service (DDoS) attacks against targets from. The attacks were all coming from compromised routers[…]
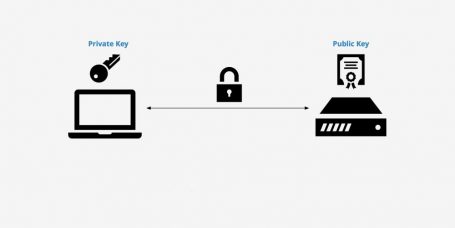
Features grab banner, detect ssh1 protocol and zlib compression; gather key-exchange, host-key, encryption and message authentication code algorithms; output algorithm information (available since, removed/disabled, unsafe/weak/legacy, etc); analyze SSH version compatibility based on algorithm information; historical information from OpenSSH and Dropbear[…]
A Penetration Testing Framework ______ ______ (_____ \ (____ \ _____) ) ____ ____ ____) ) ___ _ _ | ____/ / _ )| _ \ | __ ( / _ \ ( \ / ) | | ( (/[…]
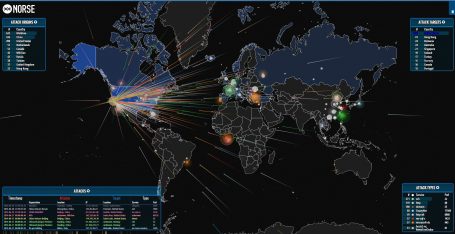
FastNetMon – A high performance DoS/DDoS load analyser built on top of multiple packet capture engines (NetFlow, IPFIX, sFLOW, SnabbSwitch, netmap, PF_RING, PCAP). What can we do? We can detect hosts in our networks sending or receiving large volumes of[…]
What is PCI DSS The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards formed in 2004 by Visa, MasterCard, Discover Financial Services, JCB International and American Express. Governed by the Payment Card Industry Security[…]
The question a wise security manager asks is, can it be done, outside of a James Bond or Mission Impossible scenario? Is it possible to hack a satellite? If you mean use the satellite for your own signals, the answer[…]
Five Questions to Ask When You’ve Been Compromised 1. Which systems and data were affected? 2. How did they do it? 3 . Who did this to us? 4. Is it really over? 5. Can it happen again? Modern security[…]
|--Although you should be able to work out who I am, I don't really care, as I can work out who you are. So beware of leaving footprints.--|